Many businesses run their IT infrastructure on a Microsoft environment. This can be the traditional onsite Active Directory to integrating with Azure and Office 365. There are many different methods that you can use for authenticating your Acumatica environment without having to use segregated Acumatica authentication.

Benefits of using external authentication
There are many benefits of using an external authentication provider rather than the built-in Acumatica authentication:
- User accounts will be created when the user first logs into Acumatica
- Use the same username and password across the board without synchronization services or Identity Management
- Roles are defined by your existing groups and mapped to Acumatica roles
- Possibility for configuring single sign-on
There are 4 main methods to integrate your Microsoft environment with Acumatica:
- Active Directory through LDAP
- Active Directory Federation Services (ADFS)
- Azure Active Directory / Office 365
- Azure AD Domain Services (DS)
Active Directory / Azure AD Domain Services
Microsoft Active Directory has been installed for many years across enterprises to provide centralized management and security of servers, workstations, and other devices. Your business may have Active Directory implemented and wish to integrate your user accounts with Acumatica. Your users will enter their username and password in the standard Acumatica login box to sign into their account.
Azure AD Domain Services is Microsoft’s application of exposing traditional Active Directory from Azure so that you can utilize traditional Active Directory protocols. You may have this enabled if you are hosting Acumatica on an Azure VM and have the server joined to Azure Active Directory through Azure AD DS. You can then connect Acumatica the same way you would if you were using on-premise AD.
Active Directory authentication works great for a self-managed environment, as you need a direct connection from Acumatica to Active Directory. Active Directory LDAP can be encrypted using SSL on port 636, but Acumatica does not support connecting through SSL. It is not recommended to expose unencrypted LDAP over the internet.
https://azure.microsoft.com/en-us/services/active-directory-ds/
Active Directory Federation Services (ADFS)
Active Directory Federation Services, or ADFS, is Microsoft’s product for integrating external applications to Active Directory using protocols like OpenID and OAuth. ADFS is a feature that is included with Windows Server.
ADFS provides single sign on functionality that can be configured with specific browsers via user agent strings as well as configuring passthrough authentication on the web browser. Acumatica can be set to automatically redirect to your ADFS server, allowing users to visit your Acumatica instance and automatically sign in. You can configure multi factor authentication providers through ADFS like Azure MFA or Duo Mobile to add an extra layer of security to your users. Single sign on with 2FA will prompt the user for their MFA token when signing into Acumatica, even if SSO is configured. Signing out of Acumatica will also sign you out of ADFS.
ADFS can be configured on premise as well as on a cloud VM to provide authentication to your users. ADFS has built-in failover, so you can configure redundancy through an ADFS farm to prevent an outage to your cloud applications when your primary site goes offline. This scenario also works great for self-hosted customers who want to continue to use authentication when their internet connection is offline.
https://docs.microsoft.com/en-us/windows-server/identity/active-directory-federation-services
Azure Active Directory Authentication (Office 365, ADAL)
Azure Active Directory has extensive third-party support for authentication of applications the same way hosted Exchange authenticates. Azure Active Directory has many features, including integrated Multi-Factor Authentication, single sign-on, reporting and logging, among other features. You do not have to maintain the infrastructure if you use Azure AD. Acumatica uses Azure Active Directory Authentication Libraries (ADAL) to communicate with Azure AD.
How are user accounts created?
Active Directory, Azure AD DS, and Azure AD ADAL supports pre-creating users from Active Directory. You can click Add Active Directory user from the Users screen to add them.
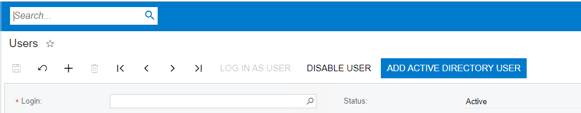
From there, you can pick the user you want to create from a selector, and it will configure read-only and hidden settings on the user like the source, as those settings are not visible on the UI.
User accounts are also created the first time a user logs in. This will also bring over the users’ groups from AD to assign roles to the users.
Currently with ADFS, you can only create users at the time they are logged in. There are no settings to create a claims authentication user from this screen. The user’s groups are brought over as well from the ADFS server as claims.
Pre-creating the user accounts allows the employee records to be mapped before the new employee logs in, rather than after. This is one of the downfalls of ADFS authentication.
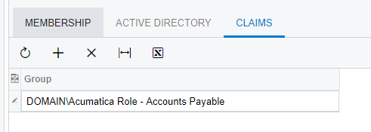
What are the differences in configuring roles?
User Roles are configured in the same place in Acumatica on different tabs, but there are more differences. Using Active Directory or Azure Active Directory Authentication, you can browse the groups on the domain or Azure to attach to a role using a selector control.
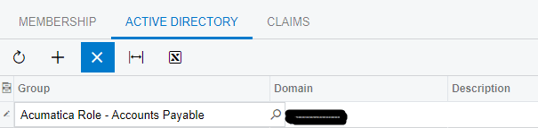
The same group added in through ADFS must be manually typed under claims. The formatting for the group would be DOMAIN\GROUP.
What are the major differences between the different authentication methods when a user wants to login?
There are a few differences in how they work, aside from how the authentication is configured.
Azure AD ADAL and ADFS authentication do not use the login form to authenticate – they use the redirection icon. You cannot use both.
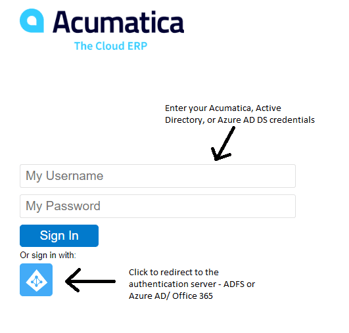
You can also enable automatic redirection to the SSO server from Acumatica. Here is an example of an environment configured for ADFS with automatic redirection.
<externalAuth authUrl=”Frames/AuthDock.ashx” silentLogin=”Federation” externalLogout=”True” selfAssociate=”True” instanceKey=”” claimsAuth=”True”>
The silentLogin states that it should redirect to the Federation server. External logout is also set so that when the user logs out of Acumatica it logs out from the authentication server and all other connected applications through the web browser.
The DeviceHub application as well as the Report Designer only support Active Directory (LDAP) and Acumatica authentication.
The Acumatica mobile app will require users to login through the Active Directory login button each time with the ADAL or ADFS methods. LDAP and built-in authentication allow the users to log back in with bio-metrics such as Face-ID on iOS, while the other methods do not. If you use ADAL, the users can select the option to stay signed in allowing them to quickly log back into the mobile app, but will not prompt with bio-metric recognition.
What if I want to use multiple types of authentication?
The settings for ADFS are shared with Azure AD ADAL, and Active Directory is shared with Azure AD ADAL. You will need to pick one, but can always use built-in Acumatica authentication at the same time.
What if I want to change the type of authentication?
The major issue with changing authentication schemes is that there are many values that have to be updated in the database that are not currently exposed in the UI. The Users table has a few attributes that would have to be changed. ExtRef maps differently between ADFS and ADAL. The username formats are also different with the different systems. This is not something that has any documented process and is currently supported by Acumatica. This would be no easy task to take on.
What solution is right for my business?
This is a loaded question as there are many factors to look at. Where Acumatica is hosted makes a big impact on your decision.
ADFS and Active Directory works great for customers who host Acumatica on premise and want access to the application internally when your internet connection goes down.
Users will be able to use the standard Acumatica login form on the web and mobile apps as without having to redirect to any other web page if you use Active Directory or Azure AD DS. These users will also be able to cache their credentials on the mobile app and login with bio-metrics.
I would only select Active Directory authentication if you have your own Active Directory servers on the same site as the Acumatica servers that you host – either on premise or in the cloud on a self-managed virtual infrastructure such as Azure.
ADFS and Azure AD ADAL allows single sign-on to Acumatica, whereas Active Directory and Azure AD DS do not.
Companies with a large deployment of DeviceHub will need to create accounts to use the application if you use ADFS or Azure AD ADAL.
If you are using Acumatica with a Software As-A Service model (SaaS), you should use either Azure AD ADAL or ADFS authentication as they communicate securely over the internet via HTTPS.
Customers who have an existing ADFS Infrastructure that integrates with Office 365/Azure or other applications may want to use their own servers.
Some customers are setup to synchronize their directories up into the cloud through Azure AD Connect in a hybrid environment, but do not have the Premium licensing. Some of the features that are not free that may cause you to think about ADFS are multi-factor authentication, password writeback, and self-service password reset. If you have Azure AD Connect but not password writeback or self-service password reset, your users will be prompted to contact IT to change their password. ADFS may be the more user friendly and cost-effective option if you do not already have Azure AD Premium in a hybrid setup.
You can review the different license tier’s features on https://azure.microsoft.com/en-us/pricing/details/active-directory/
Summary
There are a few different ways you can achieve Active Directory based authentication through Acumatica. There are many different factors that you should take into consideration when selecting your authentication platform – from user experience, Acumatica platform type, licensing, and your company’s infrastructure. There is no simple switch to change authentication methods which places more importance on this decision. I hope this blog gave enough insight to help make your decisions easier.
 Canada (English)
Canada (English)
 Colombia
Colombia
 Caribbean and Puerto Rico
Caribbean and Puerto Rico
 Ecuador
Ecuador
 India
India
 Indonesia
Indonesia
 Ireland
Ireland
 Malaysia
Malaysia
 Mexico
Mexico
 Panama
Panama
 Peru
Peru
 Philippines
Philippines
 Singapore
Singapore
 South Africa
South Africa
 Sri Lanka
Sri Lanka
 Thailand
Thailand
 United Kingdom
United Kingdom
 United States
United States