In Part 1, Brian Stevens described how Acumatica Centurion intercepts files for AI analysis. If you missed it, you can read it here.
Introduction
Although testing uploads we performed from a standard Acumatica screen and the Acumatica Mobile App were easy enough to do, Team Theta needed to prove that the methodology implemented would work no matter how files are uploaded into Acumatica. This meant that we needed a tool to act in the role of a 3rd party system using web services to push file attachments into Acumatica. These efforts focused on creating the bulk upload utility as a standalone Windows application that uses web services to upload files.
One of the amazing features of Acumatica is that the web services component is a standard feature of the application. For each screen in Acumatica, the application has an underlining web service that can be used for inserting, amending, or removing records from the application. What makes it even better is the fact that when custom screens are created, they are web service ready and a developer doesn’t need to spend much time on providing the web service endpoint methods.
Building the Core Project Components
Let’s now explore two sections of the project: one, the web method that provides a connection for 3rd party systems to use and two, the 3rd party system we used during the project – a Windows Forms application.
For our project, we required a log screen to provide system administrators information regarding file attachments when they are being uploaded to Acumatica. The log screen provides this information on the file itself and who is trying to upload it. These results are received from Centurion before being allowed to be uploaded. You can think of it as a quarantine process and logging screen for administrators.
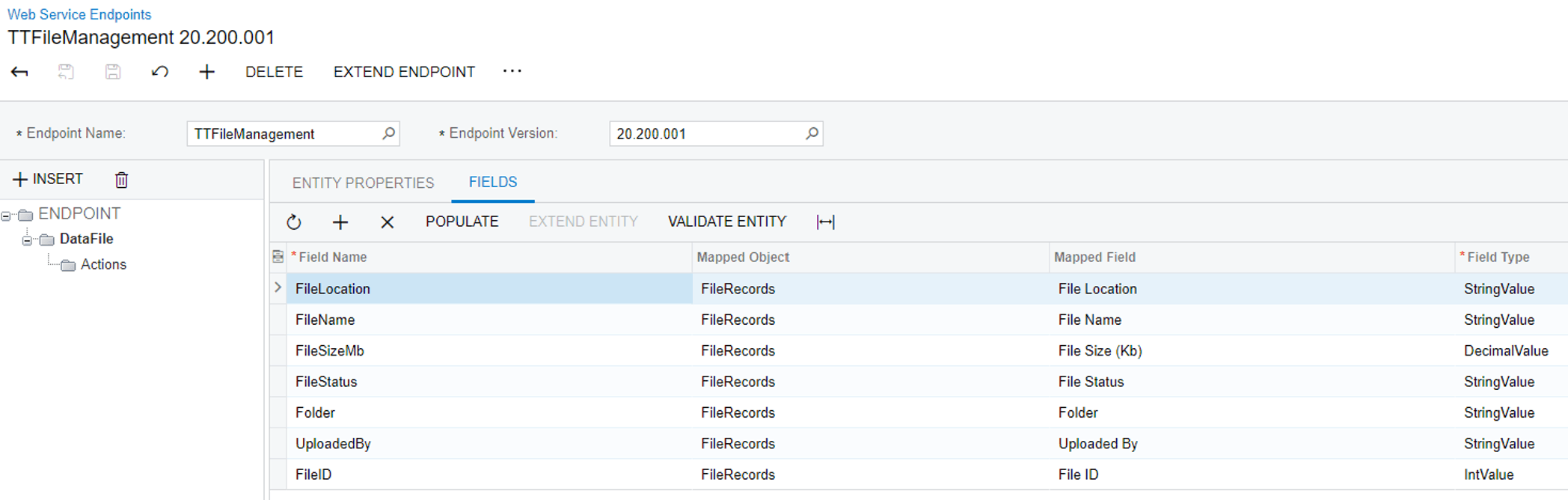
Once the screen was created and tested, the next step was to add web services. For our new web service, an endpoint was created and a custom screen Object was defined. For the object, the required fields were added and the method was now ready to be used.
Below you can see our web services endpoint and the data fields we mapped:
 Next we built a windows-based utility that would be seen as a 3rd party system. The application holds information (files) that needed to be transferred to Acumatica. For our purposes, the utility needed to read files from a folder and loads each file individually into Acumatica.
Next we built a windows-based utility that would be seen as a 3rd party system. The application holds information (files) that needed to be transferred to Acumatica. For our purposes, the utility needed to read files from a folder and loads each file individually into Acumatica.
The application utility uses the standard Microsoft Directory.GetFiles() folder to return all the file names of the folder and create a FileInfo object. When the file is read, it is converted into a byte array and moved to a memory stream. Using the memory stream, the object is sent to Acumatica using a simple PUT method of the file and linked to the log record created using the Newtonsoft.Json libraries. When the PUT method calls the Attachment methods of Acumatica, the information is submitted to Cloudmersive for further analysis and provides the results to the specified log record.
Step 1 – Getting the Files
The windows application reads the files from a specified directory to start the process for the files to be uploaded:
GIST: https://gist.github.com/Gerhard-ZA/3b67ba2ff66fdd606d930a366218583f
Step 2 – Create a Log Entry on Acumatica
Now we create the record that is used for the entry log which holds the Cloudmersive results:
GIST: https://gist.github.com/Gerhard-ZA/f99159f6002abcbc2f3a756ff0c8431e
Step 3 – Converting the File to the Memory Stream
Then each file is read from the File Stream and converted to a byte array:
GIST: https://gist.github.com/Gerhard-ZA/4fb8b62501783714fc565cef66ca1d21
Step 4 – Send the data to Acumatica, using Web Services PUT
And lastly, the memory stream data is uploaded to Acumatica.
GIST: https://gist.github.com/Gerhard-ZA/8c661c9f9723da53a4a96522db934daa
Extending the Solution
We can easily extend the solution to accomplish more useful things:
- Data migration – upload mass images from a folder system, resize and attach to inventory items
- 3rd party systems that push in EDI data and documents
- Users that take pictures for upload – verify NSFW and file size
- Scan documents uploaded for any viruses
Summary
The Acumatica xRP platform allowed us to extend easily the base system to add a use-case scenario with a set of business requirements we had agreed upon amongst our team members before we flew out to Las Vegas where the hackathon was being held. In our planning sessions, we chose a project utilizing advanced security without having to create any new patches or files that changes the core of the system itself. We simply extended Acumatica to provide access to business value we identified for our project. We were able to execute successfully our plan within the allotted time of the hackathon thanks to the great teamwork of all the members of our team – a mere 12 hours.
To learn more about our team and the other winning teams, read the 2022 Hackathon Recap post here.
Happy coding!
Team Theta Hackathon PowerPoint Presentation (PDF)