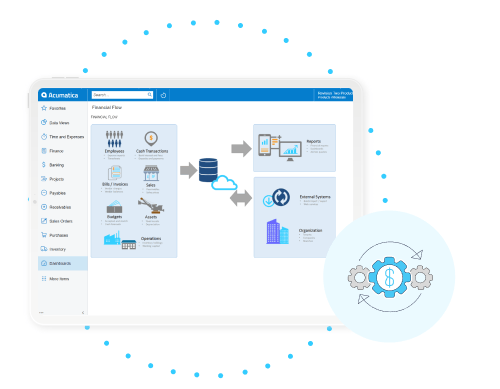
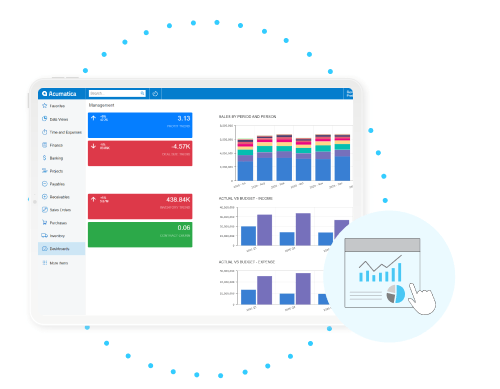
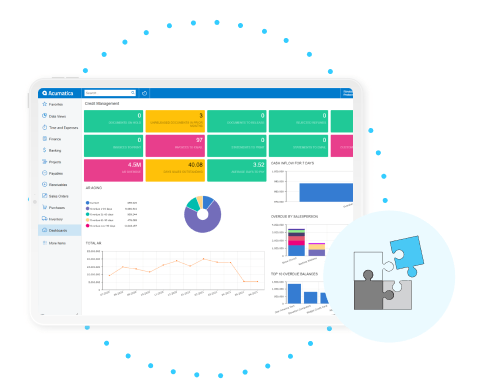
Powerful Financial Management Software, Solid Financial Management Foundation
Acumatica’s financial management software takes managing your business’ assets, income, and expenses from complex to simple with configurable processes, mobile anytime access, and best-in-class accounting applications resting on a single, future-proof platform. To operate at peak performance, let Acumatica be the backbone of every financial decision you make.
 Canada (English)
Canada (English)
 Columbia
Columbia
 Caribbean and Puerto Rico
Caribbean and Puerto Rico
 Ecuador
Ecuador
 India
India
 Indonesia
Indonesia
 Ireland
Ireland
 Malasya
Malasya
 Mexico
Mexico
 Panama
Panama
 Peru
Peru
 Philippines
Philippines
 Singapore
Singapore
 South Africa
South Africa
 Sri-Lanka
Sri-Lanka
 Thailand
Thailand
 United Kingdom
United Kingdom
 United States
United States